4 New Big Data Security Worries
The past couple of years haven’t been easy ones for cyber security specialists, especially those charged with protecting the growing reservoirs of Big Data. The headlines featured more stories about data breaches than about most any other aspect of Big Data and related technologies — even though that time period marked some impressive improvements in terms of open source software, database technology, and the growing importance of the data scientist.
But this year marks a shift. No, sorry, the data breach will still be a thing. But these threats to Big Data will be joined by a new series of threats to be aware of and to build protection against. Here are the evolving threats to your Big Data.
1. The Internet of Things
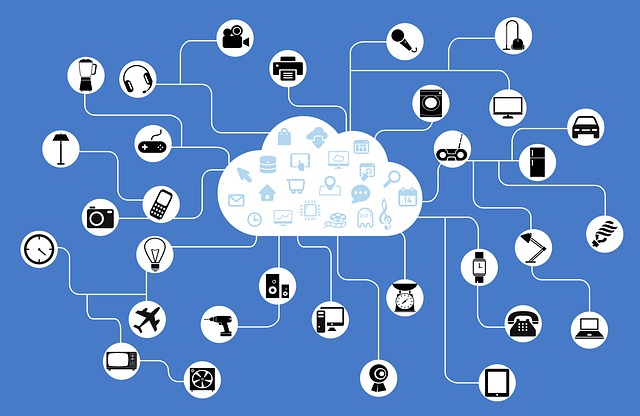
As people become more dependent on connected devices, hackers are finding new ways to exploit those devices. In some cases, it’s just about stealing the data. In other cases, it’s about altering the devices’ software for the hacker’s purposes.
The largest contributor to the growth of Big Data is connected devices, aka, the Internet of Things. In the words of a controversial public figure, the IoT is going to be HUGE. Gartner predicts that by the end of this decade, there will be a mind-boggling 21 billion connected devices. While these devices are busy making us healthier, keeping our morning commutes to work safer, and making sure that our widgets are manufactured in the most efficient possible ways — hackers are busy figuring out what kinds of mayhem they can cause. Some of the IoT hacking will be sheer mischief, while other hacks will be more serious, and potentially life-threatening.
2. Hacking Moves Beyond Mere Identity Theft
Most hacking to date has been for the sole purpose of stealing data. The majority of the stolen data is used for identity theft, or to be sold on the Dark Web for the same purpose. A small segment of it has been for the purposes of extorting or embarrassing an organization, such as in the case of the Ashley Madison hack. But the hackers emerging today aren’t just interested in charging $2,500 in electronics to an Amazon account in your name. These hackers are seeking to gain a competitive advantage (corporate espionage type hacks) or are hacking for political or social causes: hactivism. Some hacking groups are backed by terrorist organizations or various world governments, while others are doing it for sheer entertainment. Whatever the reasons, hackers are better funded, more highly skilled and specialized, and more motivated than ever before.
3. Cyber Criminals are Now Available ‘as a Service’

Hacker for Hire? You bet. They are out there, and they’re becoming more mainstream.
Lack the skills to hack your enemy yourself? That’s okay. Today’s would-be criminals can merely hire a qualified hacker to do their dirty work. If ‘cyber crime as a service‘ sounds far-fetched, you haven’t heard about Cryptolocker. This ransomware essentially locks down someone’s systems until the agree to pay up. Look for cyber crime services to become more mainstream, no longer limited to just the deep, dark recesses of the Interent.
4. The Evolving Nature of the Insider Threat
Most of the insider threats to date haven’t been of the malicious variety. The majority are limited to users who are simply ignorant or careless, plus the occasional disgruntled employee who left mad because the company wouldn’t continue to pay them to post cat photos to Facebook. But as Big Data’s value becomes greater and the reasons behind attacks grow more sophisticated and aggressive, look for the insider threat to become more nefarious, as well. Stringent hiring practices and employee monitoring with strong systems monitoring will be the only solutions for protecting against these types of threats.
